TCP/IP (Transmission Control Protocol/Internet Protocol) is the basic communication language or protocol of the Internet. It can also be used as a communications protocol in a private network (either an intranet or an extranet). When you are set up with direct access to the Internet, your computer is provided with a copy of the TCP/IP program just as every other computer that you may send messages to or get information from also has a copy of TCP/IP.
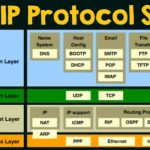
TCP/IP is a two-layer program.
The higher layer, Transmission Control Protocol, manages the assembling of a message or file into smaller packets that are transmitted over the Internet and received by a TCP layer that reassembles the packets into the original message. The lower layer, Internet Protocol, handles the address part of each packet so that it gets to the right destination. Each gateway computer on the network checks this address to see where to forward the message. Even though some packets from the same message are routed differently than others, they’ll be reassembled at the destination.
TCP/IP uses the client/server model of communication in which a computer user (a client) requests and is provided a service (such as sending a Web page) by another computer (a server) in the network. TCP/IP communication is primarily point-to-point, meaning each communication is from one point (or host computer) in the network to another point or host computer.
TCP/IP and the higher-level applications that use it are collectively said to be “stateless” because each client request is considered a new request unrelated to any previous one (unlike ordinary phone conversations that require a dedicated connection for the call duration). Being stateless frees network paths so that everyone can use them continuously. (Note that the TCP layer itself is not stateless as far as any one message is concerned. Its connection remains in place until all packets in a message have been received.)
Many Internet users are familiar with the even higher layer application protocols that use TCP/IP to get to the Internet. These include the World Wide Web’s Hypertext Transfer Protocol (HTTP), the File Transfer Protocol (FTP), Telnet (Telnet) which lets you logon to remote computers, and the Simple Mail Transfer Protocol (SMTP). These and other protocols are often packaged together with TCP/IP as a “suite.”
Personal computer users with an analog phone modem connection to the Internet usually get to the Internet through the Serial Line Internet Protocol (SLIP) or the Point-to- Point Protocol (PPP). These protocols encapsulate the IP packets so that they can be sent over the dial-up phone connection to an access provider’s modem.
Protocols related to TCP/IP include the User Datagram Protocol (UDP), which is used instead of TCP for special purposes. Other protocols are used by network host computers for exchanging router information. These include the Internet Control Message Protocol (ICMP), the Interior Gateway Protocol (IGP), the Exterior Gateway Protocol (EGP), and the Border Gateway Protocol (BGP).
TCP/IP Protocols for the Web
Web browsers and servers use TCP/IP protocols to connect to the Internet. Common TCP/IP protocols are:
i.HTTP – Hyper Text Transfer Protocol
HTTP takes care of the communication between a web server and a web browser. HTTP is used for sending requests from a web client (a browser) to a web server, returning web content (web pages) from the server back to the client.
ii.HTTPS – Secure HTTP
HTTPS takes care of secure communication between a web server and a web browser. HTTPS typically handles credit card transactions and other sensitive data.
iii.FTP – File Transfer Protocol
FTP takes care of transmission of files between computers.
TCP/IP Protocols for Email
E-mail programs use TCP/IP for sending and receiving e-mails. The TCP/IP protocols for email are:
i.SMTP – Simple Mail Transfer Protocol
SMTP takes care of sending emails. Often emails are sent to an email server (SMTP server), then to other servers, and finally to its destination. SMTP can only transmit pure text. It cannot transmit binary data like pictures, sounds or movies.
ii.MIME – Multi-purpose Internet Mail Extensions
The MIME protocol lets SMTP transmit multimedia files including voice, audio, and binary data across TCP/IP networks. The MIME protocol converts binary data to pure text, before it is sent.
iii.POP – Post Office Protocol
The POP protocol is used by email programs to retrieve emails from an email server. If your email program uses POP, all your emails are downloaded to your email program (also called email client), each time it connects to your email server.
iv.IMAP – Internet Message Access Protocol
The IMAP protocol works much like the POP protocol. The main difference is that the IMAP protocol will not automatically download all your emails each time your email program connects to your email server.
The IMAP protocol allows you to look through your email messages at the email server before you download them. With IMAP you can choose to download your messages or just delete them. This way IMAP is perfect if you need to connect to your email server from different locations, but only want to download your messages when you are back in your office.
Other TCP/IP Protocols
ARP – Address Resolution Protocol
ARP is used by IP to find the hardware address of a computer network card based on the IP address.
BOOTP – Boot Protocol
BOOTP is used for booting (starting) computers from the network.
DHCP – Dynamic Host Configuration Protocol
DHCP is used for allocation of dynamic IP addresses to computers in a network.
ICMP – Internet Control Message Protocol
ICMP takes care of error-handling in the network.
LDAP – Lightweight Directory Access Protocol
LDAP is used for collecting information about users and e-mail addresses from the internet.
NTP – Network Time Protocol
NTP is used to synchronize the time (the clock) between computers.
PPTP – Point to Point Tunnelling Protocol
PPTP is used for setting up a connection (tunnel) between private networks.
RARP – Reverse Address Resolution Protocol
RARP is used by IP to find the IP address based on the hardware address of a computer network card.
SNMP – Simple Network Management Protocol
SNMP is used for administration of computer networks.
SSL – Secure Sockets Layer
The SSL protocol is used to encrypt data for secure data transmission.
TLS – Transport Layer Security
The TLS protocol is a newer and more secure version of SSL.